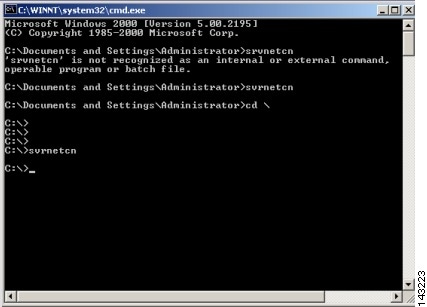
Exercise 2: Scanning with SuperScan | See What Your Attacker Sees with Scanning Tools | Pearson IT Certification

Rule to detect vulnerabilites integrating IDS and Vulnerability Scanner - ArcSight User Discussions - ArcSight
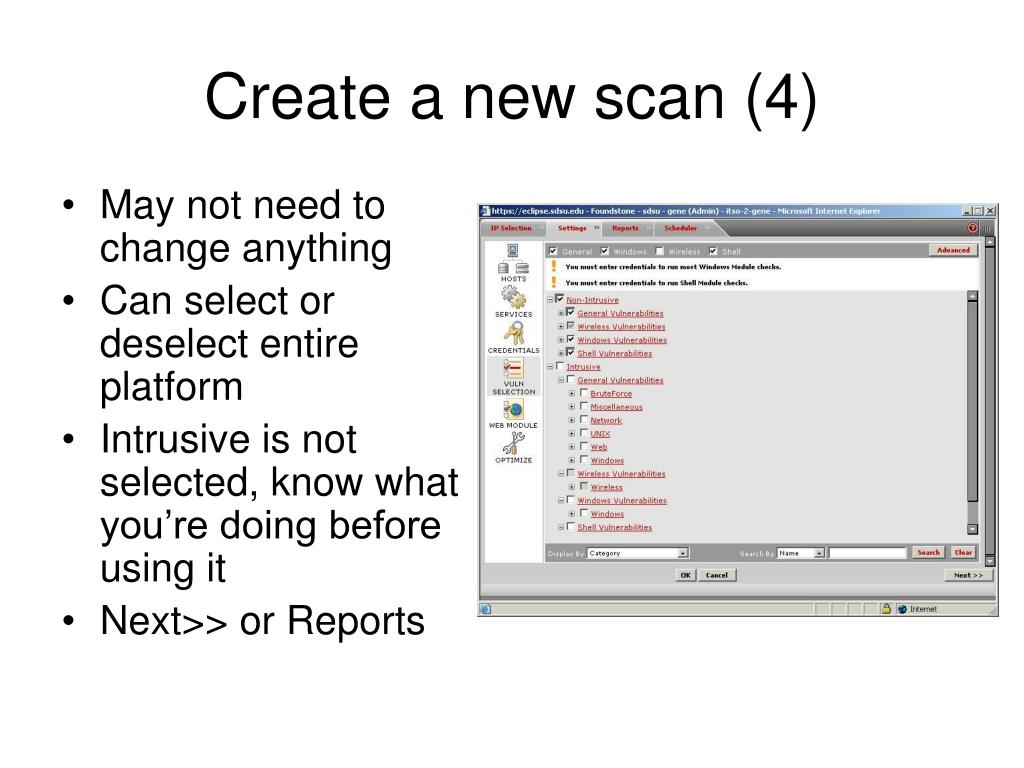
Vulnerability Management for the Real World » Successful Approaches » What is Vulnerability Management? » Challenges to Effective VM » The Problem Contents: - ppt download



![Infosecworld 08 Orlando] CSRF: The Biggest Little Vulnerability on t… Infosecworld 08 Orlando] CSRF: The Biggest Little Vulnerability on t…](https://image.slidesharecdn.com/infosecworld-08-orlando-csrf-the-biggest-little-vulnerability-on-the-web-1205423829459769-3/85/infosecworld-08-orlando-csrf-the-biggest-little-vulnerability-on-the-web-2-320.jpg?cb=1205395029)